Rockstar Games Hacked 2026
Rockstar Games has confirmed a data breach by hacking group ShinyHunters, which claims to have accessed the company’s Snowflake cloud environment by exploiting a third-party SaaS platform called Anodot. The ransom deadline is April 14 — today. ShinyHunters has already confirmed it plans to release the data after Rockstar declined to pay.
The breach is not a Rockstar-specific failure. It’s the latest hit in a rolling supply chain attack campaign that has used the same Anodot entry point to compromise dozens of large organizations.
Table of Contents
How the attack actually worked
ShinyHunters didn’t break into Rockstar directly, and it didn’t exploit a vulnerability in Snowflake, the cloud data warehouse Rockstar uses. Instead, the group went through Anodot — a SaaS platform used by enterprise teams to monitor cloud spending and detect cost anomalies.
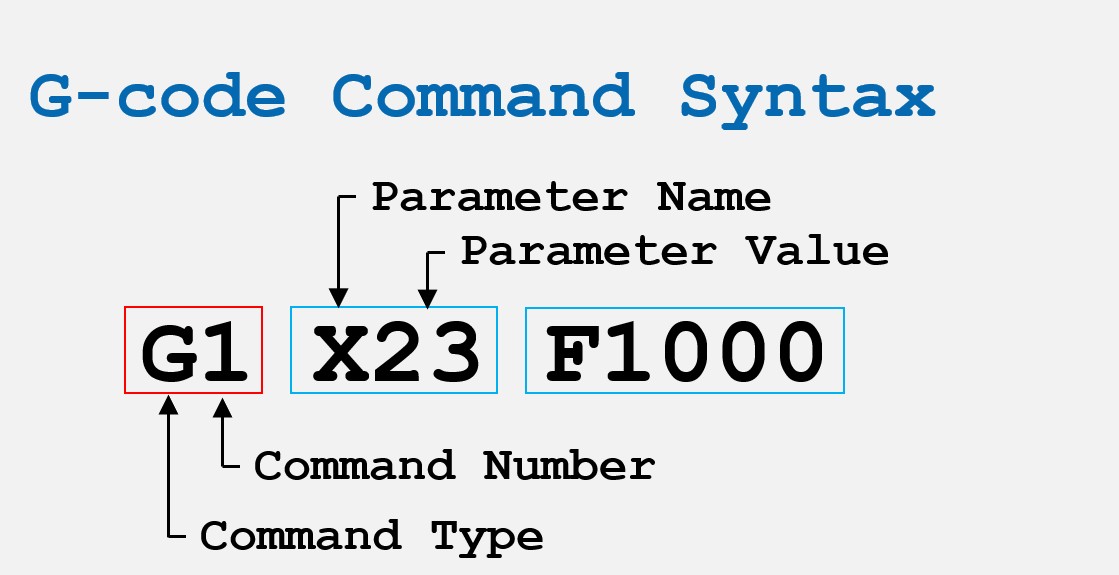
According to The Register’s analysis and Help Net Security’s reporting, the attack chain worked like this:
- Anodot’s connectors were compromised. On April 4, Anodot publicly acknowledged that its connectors were down across multiple regions — including Snowflake, Amazon S3, and Amazon Kinesis. That outage was almost certainly the visible symptom of ShinyHunters extracting authentication tokens from within Anodot’s infrastructure.
- Stolen tokens acted as valid credentials. Anodot needs access to a company’s Snowflake account to monitor cloud costs. The tokens that authenticate this connection were extracted. With those tokens, ShinyHunters could connect to Rockstar’s Snowflake environment while appearing to be a legitimate internal monitoring service.
- Rockstar’s security team saw nothing unusual. Because access came through a trusted integration with valid credentials, the traffic looked like routine background activity. The breach was functionally invisible until ShinyHunters chose to announce it.
This is the defining characteristic of modern SaaS supply chain attacks: there is no perimeter to defend against them because the attacker is, by definition, already inside as an authorized entity.
What data ShinyHunters claims to have
ShinyHunters has not published a full inventory of the stolen data, and Rockstar’s official statement to Kotaku confirmed only that “a limited amount of non-material company information” was accessed, with “no impact on our organization or our players.”
Based on what Snowflake environments typically hold for companies in Rockstar’s position, and consistent with reporting from The Verge, the data is expected to include:
- Internal financial records and budget documents
- Marketing strategies and campaign data
- Contracts with platform partners (Sony, Microsoft, retailers)
- Development pipeline data — potentially including GTA 6 release planning documents
- Cloud cost analytics data, which can expose infrastructure architecture details
No player data — passwords, payment methods, or personal information — is believed to be in scope. Snowflake data warehouses at studios like Rockstar typically store business intelligence data, not user credentials. That said, Rockstar has not confirmed the scope, and ShinyHunters has priced the full dataset at $200,000 on its dark web marketplace.
The GTA 6 question
The timing of this breach is uncomfortable for Rockstar. GTA 6 is due for release later this year and is arguably the most commercially anticipated game in the history of the medium. Any leaked data touching the game’s release window, marketing strategy, or commercial terms with Sony and Microsoft would be immediately valuable to the gaming press, competitors, and investors.
This is not Rockstar’s first breach. In 2022, a member of the LAPSUS$ group — an 18-year-old from Oxford — talked his way into Rockstar’s internal Slack channels and leaked over 90 early development videos of GTA 6 alongside source code. That attacker was later handed an indefinite hospital order under the UK Mental Health Act. The GTA 6 footage leak became one of the largest gaming leaks in history.
The 2026 breach appears structurally different — focused on corporate data rather than development assets — but Rockstar’s insistence that the data is “non-material” should be taken with appropriate skepticism. Companies consistently downplay breach scope in initial public statements, particularly when the full inventory is still unknown.
Who ShinyHunters are — and why their track record matters
ShinyHunters is a financially motivated cybercrime group active since 2020. They are not ideologically driven hacktivists. Their operational model is straightforward: identify large companies with SaaS integration gaps, extract valuable data, and apply public pressure to force payment.
Their confirmed target history, as tracked by The Record from Recorded Future, includes:
- Microsoft — claimed 500GB of source code (2020)
- Wattpad — 270 million user records
- Ticketmaster — large-scale customer data breach
- AT&T — customer and internal data
- Cisco — part of the current Salesforce/Anodot campaign
- Telus (Canadian telecom) — up to a petabyte of data claimed
- Match Group — Tinder, Hinge, OkCupid operator (January 2026)
- Salesforce-linked companies — 400+ organizations compromised in March 2026, with data from 26 already published
When ShinyHunters says it has data and sets a deadline, it typically follows through. The Rockstar ransom deadline has passed. Data publication is the expected next step.
The broader Anodot/Snowflake wave
Rockstar is not a one-off target. ShinyHunters’ current campaign is systematically exploiting the same integration trust chain — Anodot credentials being used to access downstream Snowflake accounts — across dozens of organizations simultaneously.
The Salesforce wave in March 2026 used a nearly identical pattern: a trusted third-party connector was the entry point, and the downstream damage spread across every company sharing that integration. In this case, the shared surface area is Anodot’s connector ecosystem, which serves cloud-heavy enterprises across finance, media, and technology.
NIST’s guidance on third-party risk management (SP 800-161) specifically addresses this attack class: the security of a system is only as strong as its least-privileged third-party integration. When service accounts hold long-lived authentication tokens with broad data access, a single compromised SaaS vendor can propagate access to every company it serves.
What organizations using Anodot or Snowflake should do now
Any company that uses Anodot alongside a Snowflake environment should treat this incident as a direct threat indicator. Recommended immediate actions, consistent with CISA guidance on cloud security:
Immediate (within 24 hours):
- Audit all active Snowflake authentication tokens issued to third-party integrations
- Check Anodot connector authentication logs for unusual access patterns from April 1 onward
- Rotate any Snowflake service account credentials connected to Anodot
- Review Snowflake query history for unexpected bulk exports
Short-term (within 7 days):
- Implement network policies in Snowflake to restrict which IP ranges can connect via service accounts
- Enable Snowflake’s Dynamic Data Masking for sensitive columns
- Move service account authentication from long-lived tokens to short-lived OAuth flows where possible
- Apply least-privilege principles to all third-party connector permissions — a cloud cost monitoring tool does not need read access to contracts or financial records
The core problem in attacks like this is not technical complexity. It’s that service accounts are routinely granted far more access than they need, and their tokens are rarely rotated. The Anodot connector needed to read cloud spending metrics. It did not need access to Rockstar’s full Snowflake environment. That permission scope is where the breach radius was determined.
What happens next
ShinyHunters has confirmed to CyberSec Guru — the outlet that first identified the breach — that it plans to release the data following Rockstar’s non-response. The $200,000 ransom demand has not been met.
If player data of any kind is present in the published files, Rockstar faces GDPR disclosure obligations (72-hour notification window under Article 33), potential CCPA exposure, and possible FTC scrutiny. Rockstar’s current public position — that the data is non-material and contains no player information — sets a clear benchmark against which any published files will be measured.
The Xbox Games Showcase on June 7 was already shaping up as Rockstar’s next major public communication window ahead of the GTA 6 launch. Whatever ShinyHunters releases will inform whether that window gets moved earlier.
This page will be updated as the situation develops.
FAQs: Rockstar Games Data Breach 2026
Was Rockstar Games hacked directly?
No. ShinyHunters accessed Rockstar’s Snowflake cloud environment by exploiting Anodot, a third-party cloud cost monitoring platform Rockstar uses. The attackers extracted authentication tokens from Anodot that gave them valid credentials for Rockstar’s connected Snowflake account. Snowflake itself was not breached.
Is player data at risk in the Rockstar breach?
Based on current reporting and Rockstar’s own statement, no player data — passwords, payment information, or personal details — is believed to have been accessed. Snowflake environments at studios like Rockstar typically store internal business intelligence data, not player credentials. However, Rockstar has not confirmed the full scope of what was taken.
Who are ShinyHunters?
ShinyHunters is a financially motivated cybercrime group active since 2020, known for targeting enterprise SaaS integrations and cloud environments at major companies. Previous confirmed targets include Microsoft, Ticketmaster, AT&T, Cisco, Wattpad, Telus, and Match Group. They typically ransom stolen data or sell it on dark web marketplaces.
What is the ransom deadline?
ShinyHunters set April 14, 2026 as the deadline for Rockstar to pay or face a data leak. That deadline is today. ShinyHunters has already confirmed it plans to release the data, having priced the full dataset at $200,000.
Could GTA 6 be delayed because of this breach?
Rockstar has stated the breach has no impact on its organization or operations. The 2026 breach differs from the 2022 LAPSUS$ attack, which directly leaked GTA 6 development footage. This breach appears focused on corporate and financial data rather than game development assets. Whether leaked marketing or release-window documents could create commercial pressure on the launch timeline is unknown until the data is published.
What is Anodot and why does it matter?
Anodot is a cloud cost monitoring and analytics SaaS platform used by large enterprises to track and optimize their cloud spending across providers like Snowflake, AWS, and Google Cloud. Because it needs to read data from connected cloud accounts, it holds authentication tokens for those environments. If Anodot’s own infrastructure is compromised, those tokens can be extracted and used to access every connected customer’s cloud data — which is precisely how this breach occurred.
What is Snowflake, and was it compromised?
Snowflake is a cloud-based data warehousing platform used by thousands of large enterprises to store and analyze business data. Snowflake itself was not compromised in this incident. The attackers used legitimate authentication tokens to access Rockstar’s Snowflake account as an authorized user — Snowflake’s platform behaved as intended.
What should I do if my company uses Anodot or Snowflake?
Immediately audit all third-party service account tokens connected to your Snowflake environment, rotate credentials tied to Anodot integrations, and review query logs from April 1 onward for unexpected bulk data access. CISA’s cloud security advisories and NIST SP 800-161 on third-party risk management provide the formal framework for the full remediation process.